Nicolás Georger
Self-taught IT professional driving innovation & social impact with cybernetics, open source (Linux, Kubernetes), AI & ML.

TL;DR: Imagine a world where your favorite social media platforms go dark, financial systems crash, and even space exploration grinds to a halt. This dystopian scenario almost became a reality thanks to a single leaked access token that could have given malicious actors the keys to the kingdom—the
Read the full post →

Em poucas palavras
O jardim do GitHub tem uma erva daninha de privacidade crescendo fora de controle. Acontece que excluir seus forks do GitHub ou até mesmo repositórios inteiros não apaga os dados. Essa informação suculenta permanece pronta para ser coletada, acessível a qualquer pessoa que saiba onde procurar. Estamos
Read the full post →

En Resumen
¿Alguna vez has hecho commit de algo que no deberías? Porque el jardín de GitHub tiene una maleza de privacidad creciendo sin control. Resulta que eliminar tus forks de GitHub o incluso repositorios enteros no borra realmente los datos. Esta jugosa información se mantiene fresca para ser recogida,
Read the full post →

TL;DR
Have you ever committed something you shouldn't?, Because the GitHub garden has a privacy weed growing out of control. Turns out, deleting your GitHub forks or even entire repositories doesn't actually erase the data. This juicy info stays ripe for the picking, accessible to
Read the full post →

TL;DR;
Google Cloud está causando sensación en su conferencia Cloud Next en Tokio al inyectar a su línea de bases de datos una buena dosis de IA. Spanner, su base de datos SQL distribuida, ahora cuenta con capacidades de búsqueda gráfica (graphQL) y vectorial (Vector), perfectas para aprovechar el
Read the full post →

TL;DR;
Google Cloud is making waves at its Cloud Next conference in Tokyo by injecting its database lineup with some serious AI muscle. Spanner, their globally distributed SQL database, now boasts graph and vector search capabilities, perfect for tapping into the power of generative AI. Bigtable, their NoSQL workhorse
Read the full post →

TL/DR
Grab your black hats, fellas: Wiz Research team has been poking around AI services to see if they're really as secure as they seem. They audited SAP AI Core, a PaaS which allows to develop, train and run AI managed, scalable services. Spoiler alert: They found
Read the full post →
Vamos ver quais são as diferenças chave entre um Site Reliability Engineer (SRE) e um Administrador de Sistemas (SysAdmin) "tradicional", destacando como a "filosofia" SRE, impulsionada pela automação, monitoramento e uma colaboração próxima com os desenvolvedores, leva a uma maior confiança nos sistemas e um ciclo
Read the full post →
Veamos cuáles son las diferencias clave entre un Site Reliability Engineer (SRE) y un Administrador de Sistemas (SysAdmin) "tradicional" destacando cómo la "filosofía" SRE, impulsada por la automatización, la monitorización y una estrecha colaboración con los desarrolladores, conduce a una mayor confianza en los sistemas y
Read the full post →
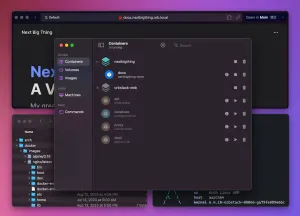
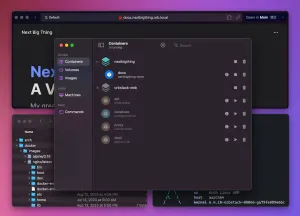
macOS users have several solid options for running containers, each with its own strengths. We review OrbStack, Lima (Linux Machines), and Docker Desktop, comparing their features, performance, and ease of use to help you choose the best fit for your development workflow. Whether you're a seasoned Kubernetes veteran
Read the full post →

TL;DR
Tired of your Kubernetes volumes disappearing like your last vacation? 😩Longhorn 1.6 is here to save your data (and your sanity)! This bad boy brings persistent volumes to your Kubernetes cluster, making sure your apps stay fed with data, no matter what chaos the internet throws at
Read the full post →
ParadeDB is shaking things up in the world of search and analytics by offering a compelling Postgres-based alternative to Elasticsearch. This article dives into ParadeDB's features, how it stacks up against Elasticsearch, and why you should keep an eye on this emerging technology.
ParadeDB: Riding the Postgres Wave
Read the full post →